15-Second summary
Profiling threat actors can require synthesizing dozens of intelligence reports across multiple sources. Threat Actor Insights Cards provide comprehensive adversary profiles that you can now query with Ask AI.
With Ask AI on Threat Actor Insights Cards, you can:
- Research adversaries faster and with more precision by asking specific questions about campaigns, TTPs, targets, or behavioral shifts. Then, verify the output through citations to the original sources in the Feedly Threat Graph.
We provide six examples to show how it can accelerate your threat actor profiling.
Overview
When a new campaign emerges or an adversary shifts tactics, you need answers fast. Threat Actor Insights Cards help consolidate intelligence about them into a single place. It looks at the most recent OSINT reports, vendor advisories, blog posts, and technical write-ups, all backed by the Feedly Threat Graph. However, you might want the data in a different format or dive deeper with specific queries.
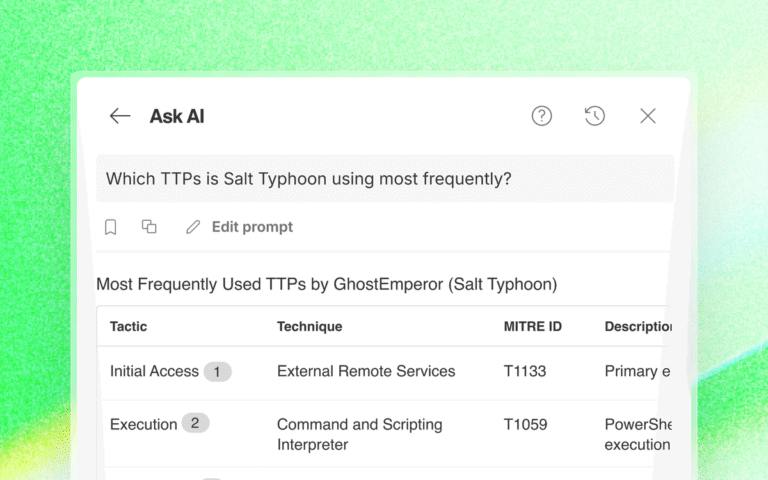
Ask AI on Threat Actor Insights Cards makes it easy to dive deeper, extract specific data, or create threat briefs in a specific format. You can ask specific questions, such as “What infrastructure has this group used in the last 90 days?” or “Which TTPs are they using most frequently?” and get precise, cited answers. The Feedly Threat Graph provides the AI with rich context, so you get precise, actionable answers in the format you need.
Example 1: Customize your executive summary
There’s no single “best” executive summary for all stakeholders. Depending on their needs, they might want it more business risk-focused or more technical. You can use Ask AI to create a summary tailored to your team or stakeholders.
Ask AI Prompt
Generate an executive summary about this Threat Actor for my CISO and the board.
Write a 4–5 sentence, non‑technical summary of the threat actor suitable for an executive threat brief, covering: who they are, what they want, who they target, and why they matter this quarter.
Avoid jargon but keep it specific and action‑oriented.nical sophistication), and Victim (sectors, geographies, selection criteria)Ask AI Response
Example 2: Diamond Model analysis
A Diamond Model is a structured way of turning raw threat data into actionable intelligence by revealing the connections that matter for detection, attribution, and defense. It can help you identify patterns across campaigns or identify pivot points for deeper analysis. Ask AI can instantly create the Diamond Model so you can focus on cross-adversary analysis.
Ask AI Prompt
Conduct a comprehensive Diamond Model analysis. Include: Adversary (attribution, motivations, capabilities), Infrastructure (domains, IPs, hosting, C2), Capabilities (malware, tools, TTPs, technical sophistication), and Victim (sectors, geographies, selection criteria).Ask AI Response
Example 3: Dive into key tactics
Often, you just want a quick analysis to understand part of the attack chain. You can simply query the Threat Actor Insights Card to find evidence of how they gained initial access, for example.
Ask AI Prompt
How did this Threat Actor gain initial access to victim environments?Ask AI Response
Example 4: Understand how behaviors are changing
Most CTI teams have identified a target list of adversaries. They understand these actors well and perform hunts for suspicious behavior. But how do you keep up with their changing behaviors? And how do you quickly develop an understanding of new threat actors who move into your space? You can use Ask AI to help you understand historical behavior patterns and how those have shifted over time.
Ask AI Prompt
Describe the historical targeting pattern of this threat actor: primary regions, industries, victim size (SMB/enterprise/government), and common initial access vectors. Highlight any changes or expansions in targeting over the last 12–24 months.Ask AI Response
Example 5: Evaluate potential risk to your organization
You hear about new threat actors all the time. In Feedly, you can even monitor for new threat actors targeting companies like yours. Now that you have identified a potential risk, how do you evaluate that risk? You can use Ask AI to analyze historical attack patterns against targets like your company and to assign a risk score, showing the factors used in that assessment.
Ask AI Prompt
Assume my organization is in the [Industry] sector and operates mainly in [Region]. Assess the relevance and risk of this threat actor to my environment. Rate overall risk (1-10) and list the 3 most relevant factors driving that assessment.Ask AI Response
Example 6: Create intelligence that your SOC can act on now
Arm your SOC team with the technical intelligence elements they need to implement defenses quickly.
Ask AI Prompt
Given what is publicly known about this threat actor’s TTPs, list 5 concrete detections,monitoring, or mitigations a SOC can implement within 1–2 weeks. Reference specific behaviors (e.g., known lateral movement style, C2 patterns) rather than just generic technique names. Include IoCs, detection rules, or any other details to help them take actionAsk AI Response
Get answers, not just data
Try Ask AI in Threat Actor Insights Cards and extract the exact intelligence you need, with citations to verifiable sources.
Start Free Trial